der ccc prangert offiziell auf seiner homepage die praxis der firma canon an, die bei jedem ausdruck versteckte daten über den drucker aufs papier schickt. wenn ich das bisher jemandem erzählt habe, wurde ich meistens nur schräg angesehen. glaubt was ihr wollt, aber checkt vorher die story über den „drucker-code“:
„Cory Doctorow: Many color laser printers hide information about your printer’s serial number and the date and time of your print job in every job you print. It’s believed that this is done to get your equipment to incriminate you without your knowledge. Now EFF has decoded the information-hiding scheme on the Xerox Docucolor series, by getting EFF supporters to print out pages from their printers and mail them to our researchers, who examined them under magnification and special light and cracked the code.
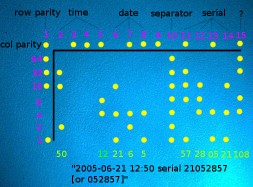
The DocuColor series prints a rectangular grid of 15 by 8 miniscule yellow dots on every color page. The same grid is printed repeatedly over the entire page, but the repetitions of the grid are offset slightly from one another so that each grid is separated from the others. The grid is printed parallel to the edges of the page, and the offset of the grid from the edges of the page seems to vary. These dots encode up to 14 7-bit bytes of tracking information, plus row and column parity for error correction. Typically, about four of these bytes were unused (depending on printer model), giving 10 bytes of useful data. Below, we explain how to extract serial number, date, and time from these dots. Following the explanation, we implement the decoding process in an interactive computer program.
Because of their limited contrast with the background, the forensic dots are not usually visible to the naked eye under white light. They can be made visible by magnification (using a magnifying glass or microscope), or by illuminating the page with blue instead of white light. Pure blue light causes the yellow dots to appear black. It can be helpful to use magnification together with illumination under blue light, although most individuals with good vision will be able to see the dots distinctly using either technique by itself.“
[via]















